Market drawdowns dominate headlines. Charts turn red. Volatility becomes the villain. Yet across digital asset markets, a quieter and often permanent loss continues to compound, unnoticed and uncounted.
Access disappears. Private keys are misplaced. Seed phrases are lost. Passwords expire. Devices fail. Heirs are locked out. In many cases, the asset still exists on-chain, untouched and provably owned. The value was never destroyed. The access was.

This distinction matters. For self-custodied holders, crypto access risk represents a structural threat that behaves very differently from price volatility. Markets recover. Access failures do not. As digital assets mature into long-term holdings rather than speculative trades, this risk is becoming one of the most material yet least discussed dimensions of ownership.
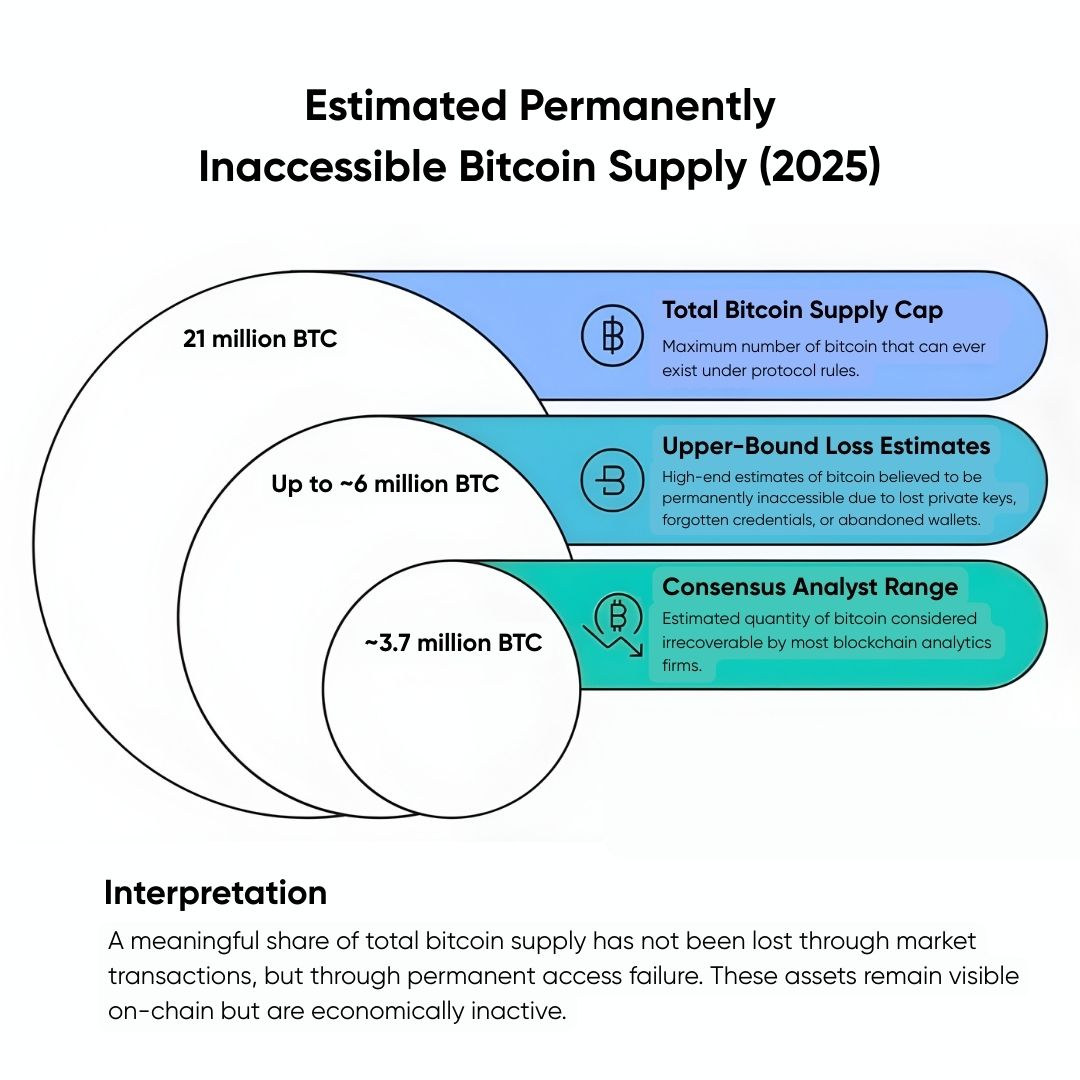
How Much Crypto Is Already Lost
Estimates vary, but the numbers are not trivial. Multiple blockchain analytics firms have suggested that between 15 and 20 percent of all Bitcoin may be permanently inaccessible due to lost keys. That represents millions of coins, not sold, not transferred, simply frozen by missing credentials.
Ethereum, while more flexible in tooling, faces similar challenges. Lost wallets, forgotten passwords, and inaccessible multisig configurations quietly accumulate with each cycle. These losses rarely make the news. There is no liquidation event. No bankruptcy filing. No visible transaction. The asset just stops participating in the economy.
For investors focused on long-term investment in digital assets, this introduces a paradox. Assets designed to be censorship-resistant and immutable also offer no recovery mechanism when access planning fails.
Volatility Is Temporary. Access Failure Is Permanent.
Price risk is emotional. Access risk is final. A market drawdown tests patience. An access failure ends ownership. Yet most investors spend far more time managing volatility exposure than planning for access continuity.
This imbalance stems from familiarity. Investors understand market risk because traditional finance has conditioned them to expect it. Access risk feels operational, almost mundane. Passwords can be reset. Accounts can be recovered. In crypto, that assumption does not hold. Self-custody replaces institutional recovery processes with personal responsibility. Without explicit planning, responsibility becomes fragility.
This is why digital asset key loss disproportionately affects long-term holders. The longer assets sit untouched, the more likely credentials degrade. Devices are upgraded. Storage methods are forgotten. Documentation is misplaced. Life intervenes. Ironically, inactivity, often praised as disciplined investing, can amplify access risk if governance is absent.
Self-Custody Shifts Risk, It Does Not Remove It
Self-custody is frequently framed as risk reduction. No counterparty. No custodian failure. No withdrawal freeze. That framing is incomplete. Self-custody removes counterparty risk but introduces continuity risk. The asset survives independently of institutions, but access depends entirely on the owner’s operational rigor.
In institutional settings, access is layered. Controls exist for recovery, succession, and redundancy. In individual self-custody, those layers must be designed intentionally. This is why firms offering consulting on digital asset management increasingly emphasize governance alongside security. Hardware wallets and multisig setups solve only part of the problem. They protect against theft. They do not protect against forgetfulness, incapacity, or time.
The Inheritance Blind Spot
One of the most severe access risks emerges not from negligence but from mortality. A growing portion of digital assets is held by individuals with no documented succession plan. In traditional finance, estates rely on custodians, courts, and legal frameworks to transfer ownership. In self-custody, none of these mechanisms function without prior preparation.
If no one else knows how to access the keys, assets remain locked forever. This reality is already reshaping conversations among digital asset advisory services providers. Estate planning for digital assets is no longer niche. It is foundational. Yet surveys consistently show that a majority of self-custodied holders have not shared recovery instructions with any trusted party. Many have not written them down at all. The result is predictable. Value remains on-chain, visible but unreachable.
Why This Risk Is Underestimated by Sophisticated Investors
Access risk persists even among experienced market participants. Sophisticated investors often assume that technical competence equals access resilience. It does not. Technical setups grow complex over time. Multisig arrangements involve multiple devices, locations, and signers. One failure point can block the entire structure. Complexity without documentation increases fragility.
This is where best practices in digital asset consulting diverge from retail advice. The goal is not maximum security features. It is durable access under stress, time, and transition. A setup that works flawlessly today may fail quietly ten years later if it depends on memory, specific devices, or undocumented procedures.
Access Risk vs Market Risk in Portfolio Construction
Traditional portfolio theory treats assets as liquid and accessible by default. Digital assets break that assumption. For those involved in investment analysis and portfolio management, this has implications. Exposure sizing should account not only for price volatility but also for access durability. A perfectly hedged position is irrelevant if it cannot be accessed when needed.
Institutions address this through custody arrangements, operational controls, and redundancy. Individual and small institutional holders often do not. As a result, access risk becomes an unpriced variable. It does not show up in models. It does not affect expected return. But it directly affects realized ownership.
The Role of Planning Over Tools
Much of the crypto security conversation focuses on tools. Hardware wallets. Cold storage. Encrypted backups. Tools matter. Planning matters more.
Access planning includes documentation, redundancy, trusted parties, and periodic review. It acknowledges that circumstances change. People move. Devices fail. Relationships evolve. This is where secure digital asset consulting solutions increasingly focus their effort. Not on selling products, but on helping holders design systems that survive boredom, neglect, and life events. A secure setup that no one can access is not secure. It is inert.
DeFi Adds another Layer of Access Fragility
Decentralized finance introduces additional access dependencies. Smart contract permissions. Protocol-specific keys. Governance tokens. Wallet integrations. For participants navigating DeFi finance assets with consultants, access risk multiplies. Losing a wallet may mean losing collateral positions, governance rights, or yield streams, even if the underlying asset remains intact.
DeFi positions often require active maintenance. Yet the keys that control them are subject to the same fragility as any self-custodied asset. As DeFi matures, access planning becomes inseparable from risk management.
Why This Matters More in 2025 and Beyond
Digital assets are transitioning from speculative instruments to long-duration holdings. Institutional interest is rising. Retail holders are aging with their assets. Time amplifies access risk. As holdings mature, inactivity increases. Attention fades. That is when access failures occur.
For a global digital asset consulting firm, this shift changes the conversation. The question is no longer how to enter markets efficiently. It is how to remain an owner across decades. Market cycles will continue. Prices will fluctuate. But access failures compound silently.
Reframing Risk in the Digital Age
In traditional finance, losing access is rare. In digital assets, it is common. This inversion demands a new mental model. Ownership is not guaranteed by possession alone. It is maintained through ongoing governance.
For investors focused on risk management in crypto investments, this means treating access as a first-class risk, alongside volatility, liquidity, and counterparty exposure. Ignoring it does not reduce it. It only delays its consequences.

Access as a Form of Discipline
There is a parallel between access planning and long-term discipline. Both require thinking beyond the current cycle. Both resist urgency. Both feel unnecessary until they are not, a concept well-understood in Crypto asset management.
Access planning is unglamorous. It produces no immediate return. Yet it preserves the possibility of all future returns. That alone should elevate its importance, especially when combined with careful Investment analysis and portfolio management to guide strategic decisions.
Designing for Durable Ownership
Kenson Investments examines how digital asset ownership evolves across market cycles, life events, and institutional adoption, working with clients as a trusted Crypto investment company. Through research and analysis, Kenson explores the operational, behavioral, and structural factors, including RWA tokenization investment opportunities, that determine whether value is merely held or truly preserved. Understanding access risk is not about fear. It is about acknowledging the need to enhance ROI with digital asset consulting.
Disclaimer: The information provided on this page is for educational and informational purposes only and should not be construed as financial advice. Crypto currency assets involve inherent risks, and past performance is not indicative of future results. Always conduct thorough research and consult with a qualified financial advisor before making investment decisions.
“The crypto currency and digital asset space is an emerging asset class that has not yet been regulated by the SEC and the US Federal Government. None of the information provided by Kenson LLC should be considered as financial investment advice. Please consult your Registered Financial Advisor for guidance. Kenson LLC does not offer any products regulated by the SEC, including equities, registered securities, ETFs, stocks, bonds, or equivalents.”